Crypto4A is Quantum-Safe Now Ask the right questions! The FIPS 140-3 Validation of a classic HSM does not make it quantum-safe A classic HSM providing PQC algorithm support does...
Inside Sco-op: life at Crypto4A From their career aspirations to personal hobbies, experiences and perspectives, get to know our latest co-op students and their journey with Crypto4A so far. ...
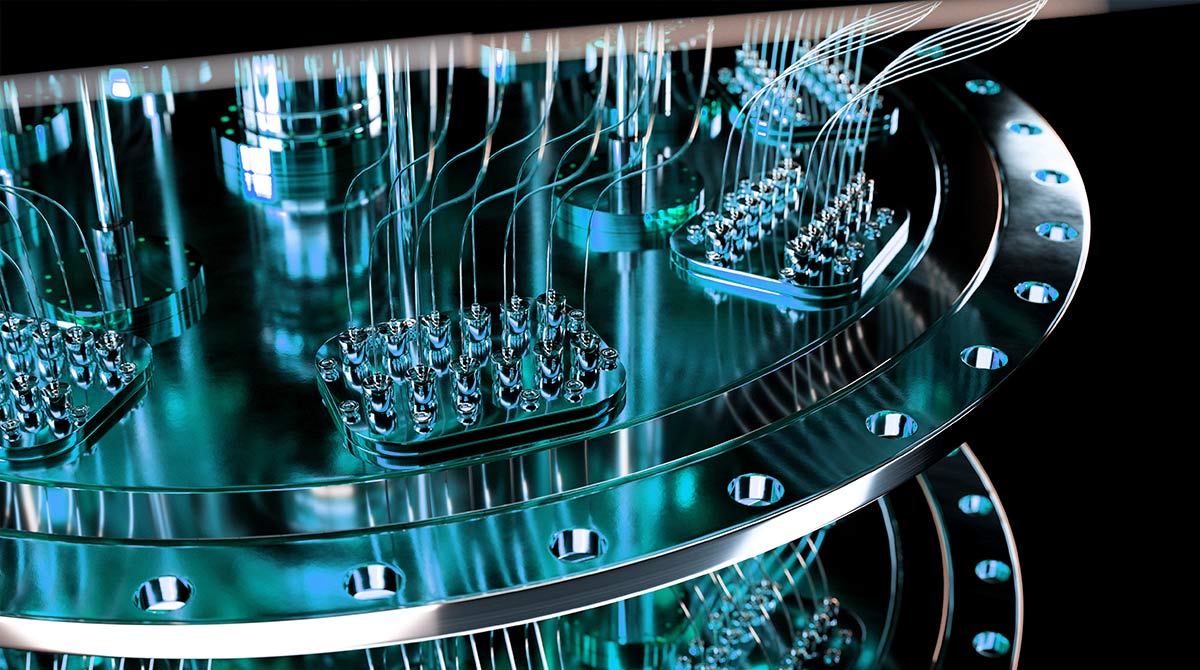
Article by Michela Menting, Senior Research Director at ABI Research. The Hardware Security Module (HSM) market has been undergoing some transformative changes in the last couple of years. From...
Crypto4A sets itself apart from competitors in a belief in simplified, predictable, and transparent hardware security module pricing for our customers. When making an important purchase such as a...
Video transcript: check out this video to understand how hybrid certificates help with post-quantum transition with an analogy from Crypto4A Hello everyone. My name is John O’Connor, VP of...
Just today NIST released its long-awaited report on the results of their Round 3 process for selecting post-quantum algorithms for standardization. The chosen algorithms CRYSTALS – Kyber, CRYSTALS- Dilithium,...
Recently, the Biden White House issued an Executive Order about the new visibilities and actions required by US government departments within a 6-month window, for an inventory of cryptography that is currently not...
We have been stressing the fact that we all need to consider the time, effort and risk involved in a change of cryptographic families on the whole of our...
In this blog, we will start to outline some thoughts on approaches for the current and coming crypto issues and how these will begin to impact our IT projects,...
This concern of “harvest now, decrypt later” has been around for many years and has been discussed by many experienced people from several perspectives – it is a real...